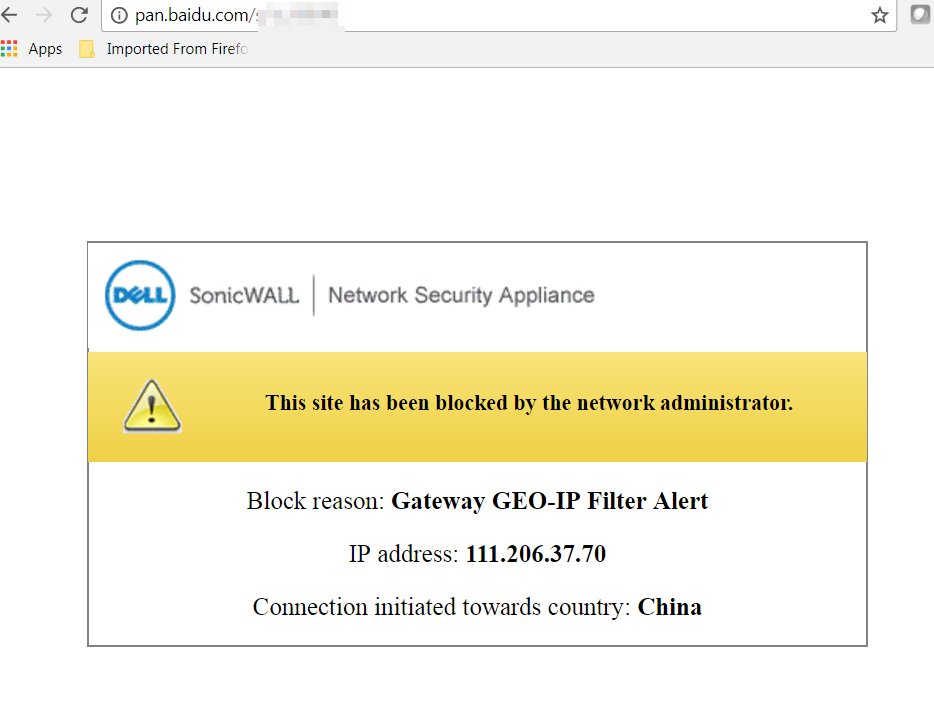
bunnie on Twitter: "wtf baidu is blocked inside the masonic temple #sketching17 https://t.co/rNFQQZMIy8" / Twitter
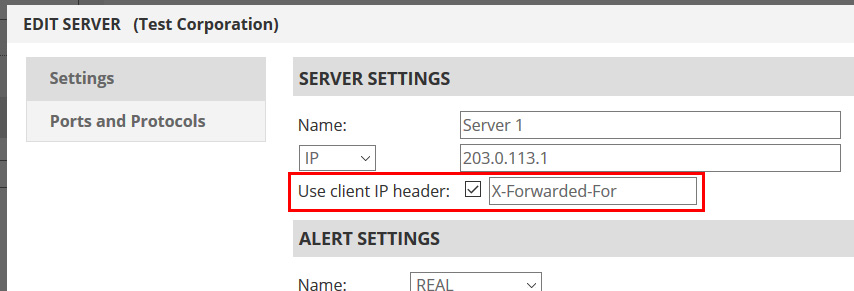
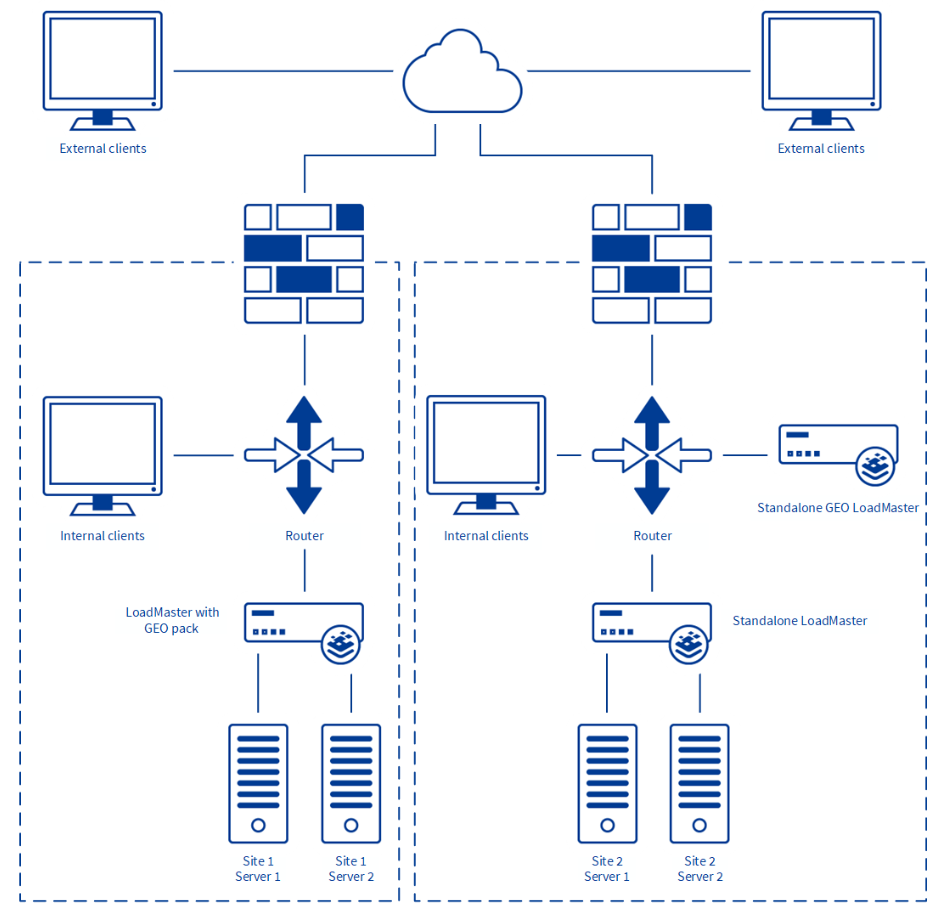
How can I obtain the original client IP address? All connections from the cloud load balancer seem to come from the same few IP addresses | Total Uptime®
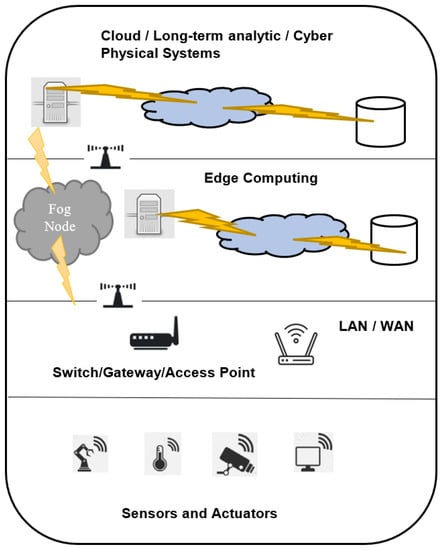
Systems | Free Full-Text | Protection Schemes for DDoS, ARP Spoofing, and IP Fragmentation Attacks in Smart Factory
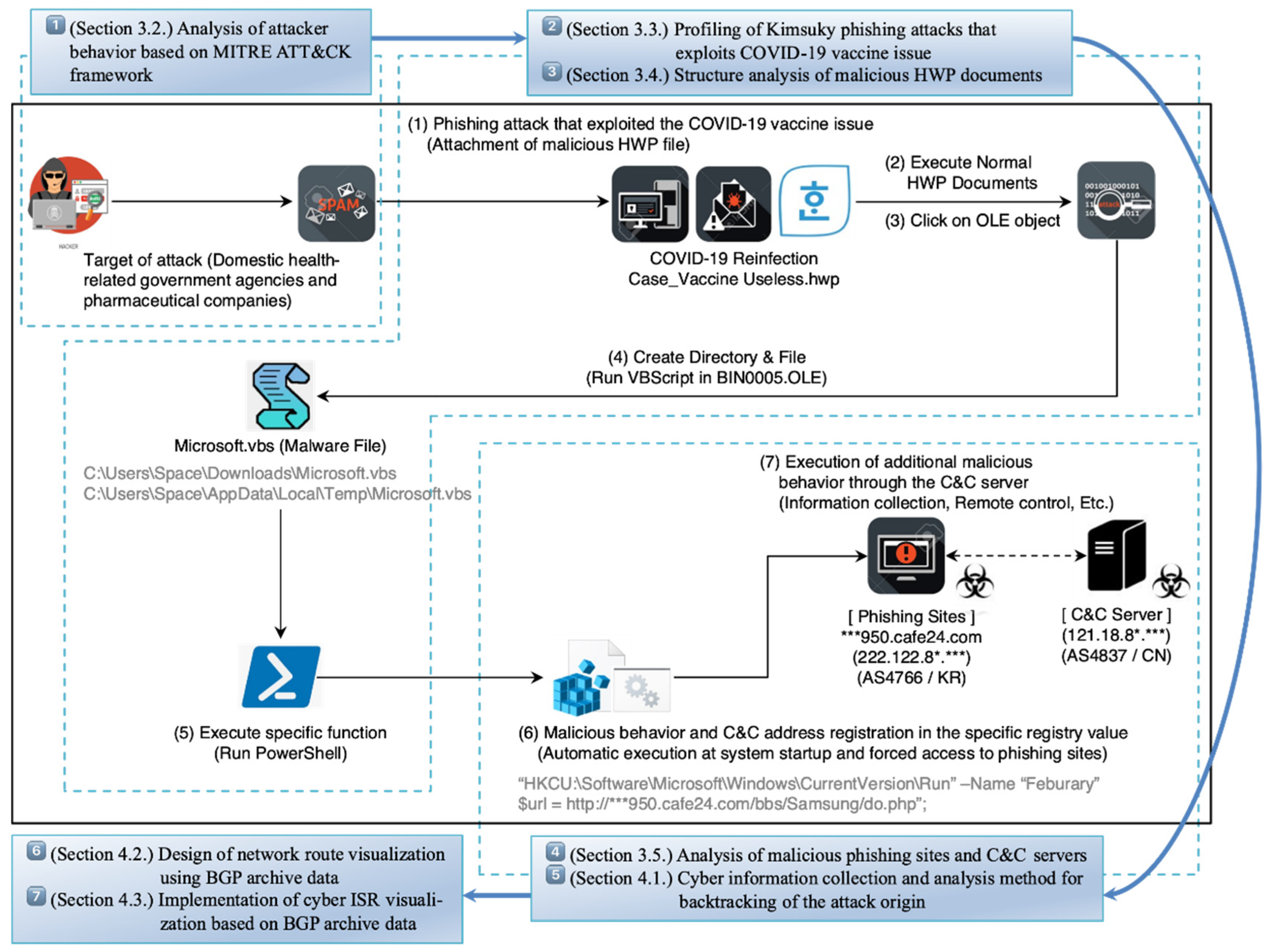
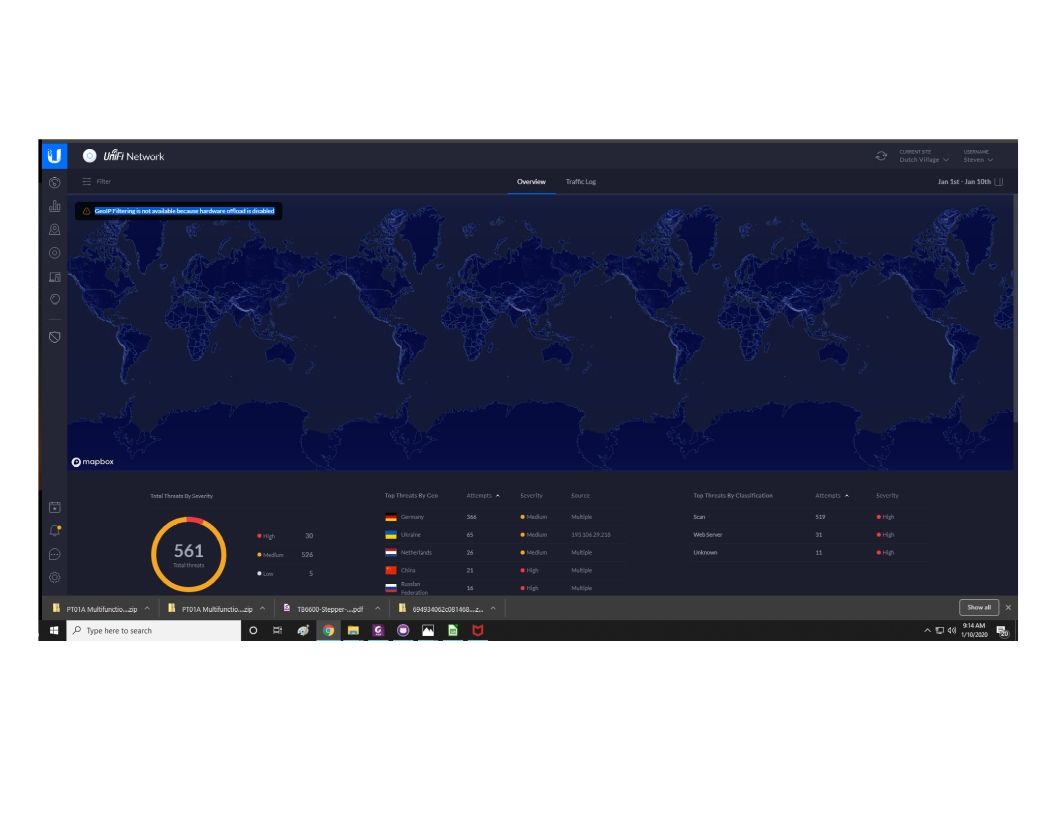
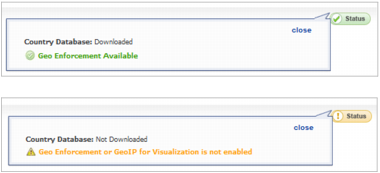
Electronics | Free Full-Text | Research on Cyber ISR Visualization Method Based on BGP Archive Data through Hacking Case Analysis of North Korean Cyber-Attack Groups





![SOLVED] Unblock a Site From SonicWall SOLVED] Unblock a Site From SonicWall](https://content.spiceworksstatic.com/service.community/p/post_images/0000061027/54986953/attached_image/Untitled.png)